VPN Security Audits Why They Matter for Your Protection
Learn why independent security audits are crucial for VPNs. Understand how these audits verify a VPN's claims and enhance your trust.

VPN Security Audits Why They Matter for Your Protection
Understanding VPN Audits What Are They Exactly
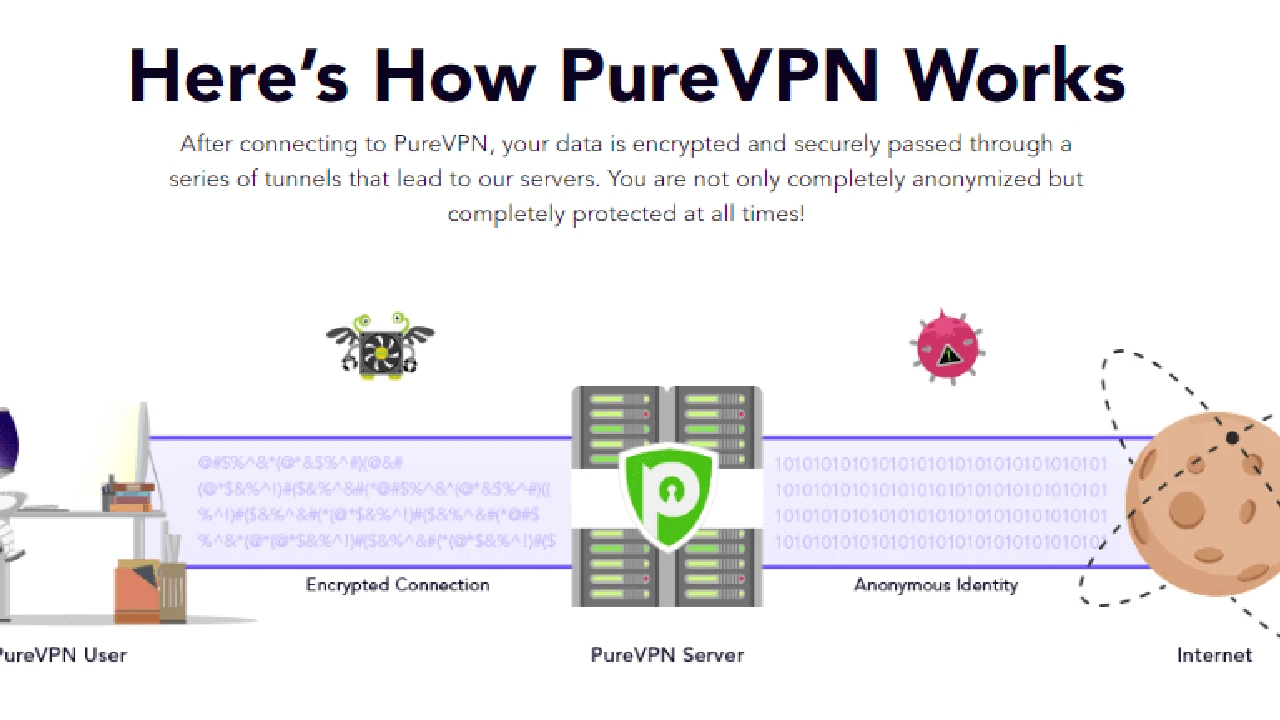
So, you’re looking for a VPN, right? You’ve probably seen a bunch of providers claiming to be the ‘most secure’ or have a ‘strict no-logs policy.’ But how do you really know if they’re telling the truth? That’s where VPN security audits come into play. Think of an audit as a deep dive into a VPN provider’s systems, policies, and infrastructure, performed by an independent third party. It’s like having a trusted expert peek under the hood of a car to make sure everything is running as it should, rather than just taking the salesperson’s word for it.
These audits aren't just about checking a box. They’re comprehensive evaluations that scrutinize everything from a VPN’s server configurations and encryption protocols to its privacy policies and internal practices. The goal? To verify that the VPN provider actually lives up to its promises, especially when it comes to protecting your data and privacy. In an industry where trust is paramount, independent audits offer a level of transparency and accountability that self-proclaimed assurances simply can’t match.
Why Independent Audits Are Crucial for VPN Trust and Transparency
Let’s be real: the VPN market is crowded. Every provider wants your business, and they all make big claims about security and privacy. Without independent verification, it’s hard to distinguish between genuine commitment and clever marketing. This is precisely why independent audits are so crucial. They act as a neutral arbiter, providing an unbiased assessment of a VPN’s security posture and privacy practices.
When an audit is conducted by a reputable third-party firm, it adds a significant layer of credibility. These firms have no vested interest in the VPN provider’s success, meaning their findings are more likely to be objective and truthful. This transparency helps build trust between the VPN provider and its users, assuring you that your sensitive data is in safe hands. It’s not just about finding flaws; it’s about confirming that the VPN’s infrastructure is robust, its policies are sound, and its claims are verifiable.
Types of VPN Audits What Gets Examined
Not all audits are created equal, and different types focus on various aspects of a VPN service. Understanding these can help you appreciate the depth of scrutiny a provider undergoes:
No Logs Policy Audits Verifying User Data Protection
This is perhaps the most talked-about type of audit. A ‘no-logs policy’ is a cornerstone of VPN privacy, meaning the provider doesn’t record your online activities, IP address, connection timestamps, or bandwidth usage. But how do you know they’re actually adhering to it? A no-logs audit involves forensic examination of a VPN’s servers, databases, and internal systems to confirm that no user-identifiable data is being collected or stored. Auditors look for any evidence of logging, review internal policies, and interview staff to ensure compliance. For example, Deloitte has audited NordVPN’s no-logs policy multiple times, providing public reports that confirm their claims. This gives users peace of mind that their online activities remain private.
Security Infrastructure Audits Assessing System Vulnerabilities
Beyond logging, a VPN’s entire infrastructure needs to be secure. Security infrastructure audits delve into the VPN’s server network, software, encryption protocols, and overall system architecture. Auditors look for vulnerabilities, misconfigurations, and potential backdoors that could be exploited by malicious actors. This includes penetration testing, where ethical hackers try to breach the system to identify weaknesses. Firms like Cure53 are well-known for their expertise in this area, having conducted security audits for several top-tier VPNs, including ExpressVPN and Surfshark. These audits ensure that the VPN’s defenses are robust against cyber threats.
Application and Client Audits Ensuring Software Integrity
Your VPN client software is your direct interface with the VPN service. If it has vulnerabilities, your security could be compromised. Application and client audits focus on the VPN apps across different platforms (Windows, macOS, Android, iOS, Linux) to ensure they are secure, free from bugs, and don’t leak any sensitive information. This includes examining the code for potential flaws, verifying encryption implementation, and checking for DNS or IP leaks. Again, Cure53 has performed extensive audits on VPN applications, helping providers identify and fix issues before they can be exploited. This ensures that the software you use to connect to the VPN is as secure as the network itself.
Key Audit Firms and Their Contributions to VPN Security
When it comes to VPN audits, certain firms have established themselves as leaders in the field, known for their rigorous methodologies and unbiased reporting. Here are a few prominent ones:
PricewaterhouseCoopers PwC A Global Leader in Assurance Services
PwC is one of the 'Big Four' accounting firms globally, and their involvement in VPN audits lends significant credibility. They bring a wealth of experience in financial and operational audits, which translates well into assessing the integrity of a VPN's systems and policies. PwC has notably audited ExpressVPN's no-logs policy, confirming their claims about not storing user activity or connection logs. Their reports are thorough and publicly available, offering a high level of assurance to users. The fact that a firm of PwC's stature is willing to put its name behind a VPN's claims speaks volumes about the provider's commitment to transparency.
Deloitte A Trusted Name in Professional Services
Another 'Big Four' firm, Deloitte, also plays a crucial role in the VPN audit landscape. They offer a wide range of professional services, including cybersecurity and risk assessment. Deloitte has been instrumental in auditing NordVPN's no-logs policy, conducting multiple comprehensive reviews of their infrastructure and practices. These audits have consistently verified NordVPN's commitment to user privacy, providing detailed reports that outline their findings. Deloitte's involvement helps to set a high standard for transparency and accountability within the VPN industry.
Cure53 A Specialist in Penetration Testing and Security Audits
Cure53 is a German cybersecurity firm renowned for its expertise in penetration testing and source code audits. Unlike the broader assurance services offered by PwC and Deloitte, Cure53 specializes in deep technical security assessments. They have conducted numerous audits for various VPN providers, including ExpressVPN, Surfshark, and TunnelBear, focusing on their applications, infrastructure, and specific features. Cure53's reports are highly detailed, often identifying specific vulnerabilities and recommending fixes. Their work is invaluable for ensuring the technical robustness of a VPN service, making sure that the software and systems are truly secure against attacks.
Versprite A Cybersecurity Consulting and Assurance Firm
Versprite is another reputable firm that provides cybersecurity consulting and assurance services, including independent audits for VPN providers. They focus on helping companies build and maintain secure systems. Versprite has audited ProtonVPN's no-logs policy and security infrastructure, confirming their strong privacy and security posture. Their audits often involve a combination of technical assessments and policy reviews, providing a holistic view of a VPN's security. Versprite's contributions help users trust that their chosen VPN has undergone rigorous scrutiny by security experts.
Recommended VPNs with Recent Independent Audits and Their Pricing
Choosing a VPN that has undergone recent independent audits is a smart move for anyone serious about their online privacy and security. Here are some top recommendations, along with their key features, typical use cases, and pricing information:
ExpressVPN A Leader in Audited Security and Performance
- Key Features: TrustedServer technology (RAM-only servers), strong AES-256 encryption, audited no-logs policy (by PwC), Lightway protocol for speed and security, kill switch, split tunneling, wide server network in 94 countries.
- Use Cases: Ideal for streaming geo-restricted content (Netflix, Hulu, BBC iPlayer), secure torrenting, bypassing censorship, and general privacy protection. Its speed makes it excellent for gaming and large downloads.
- Audit Details: ExpressVPN has undergone multiple audits by PwC for its no-logs policy and by Cure53 for its Lightway protocol and browser extensions. These audits consistently confirm their security claims.
- Pricing: Typically starts around $6.67/month for a 12-month plan (often includes 3 extra months free). Monthly plans are usually around $12.95. They offer a 30-day money-back guarantee.
NordVPN Extensive Audits and Robust Security Features
- Key Features: Double VPN, Onion over VPN, Threat Protection (ad blocker, malware protection), audited no-logs policy (by Deloitte and PwC), NordLynx protocol (based on WireGuard), kill switch, DNS leak protection, large server network.
- Use Cases: Excellent for enhanced privacy, bypassing strict censorship, secure browsing, and streaming. Its Threat Protection feature adds an extra layer of security against online threats.
- Audit Details: NordVPN has been audited multiple times by Deloitte and PwC for its no-logs policy, with public reports confirming their adherence. Cure53 has also audited their applications.
- Pricing: Often has promotional deals, with 2-year plans starting around $3.29/month. Monthly plans are typically $11.99. They also offer a 30-day money-back guarantee.
Surfshark Unlimited Devices and Audited Infrastructure
- Key Features: Unlimited simultaneous connections, CleanWeb (ad blocker, malware protection), Bypasser (split tunneling), MultiHop (double VPN), audited no-logs policy (by Cure53 and Deloitte), WireGuard protocol, kill switch.
- Use Cases: Perfect for families or individuals with many devices, streaming, secure browsing, and torrenting. Its unlimited connections offer great value.
- Audit Details: Surfshark has had its no-logs policy audited by Cure53 and Deloitte, and its server infrastructure has also been audited by Cure53, confirming its security and privacy claims.
- Pricing: Very competitive, especially for longer plans. A 2-year plan can be as low as $2.29/month. Monthly plans are around $12.95. Comes with a 30-day money-back guarantee.
ProtonVPN Strong Privacy Focus and Audited Transparency
- Key Features: Secure Core (multi-hop through hardened servers), NetShield Ad-blocker, audited no-logs policy (by Securitum and Versprite), open-source apps, strong encryption, based in Switzerland (strong privacy laws).
- Use Cases: Ideal for journalists, activists, and anyone requiring the highest level of privacy and security. Excellent for bypassing censorship and protecting sensitive communications.
- Audit Details: ProtonVPN has undergone comprehensive audits by Securitum and Versprite for its no-logs policy and overall security infrastructure, with all apps being open-source and regularly audited.
- Pricing: Offers a free tier with limited features. Paid plans start around $4.99/month for a 2-year plan. Monthly plans are typically $9.99. They also have a 30-day money-back guarantee.
TunnelBear User-Friendly and Regularly Audited
- Key Features: User-friendly interface, GhostBear (obfuscation), VigilantBear (kill switch), audited no-logs policy (by Cure53), strong encryption.
- Use Cases: Great for beginners and casual users who prioritize ease of use and basic privacy. Good for bypassing light censorship and general browsing.
- Audit Details: TunnelBear is notable for being one of the first VPNs to commit to annual independent security audits of its entire service, conducted by Cure53. These audits are publicly available.
- Pricing: Offers a limited free plan (500MB/month). Paid plans start around $3.33/month for a 3-year plan. Monthly plans are typically $9.99.
The Audit Process What Happens During a VPN Security Audit
Ever wondered what actually goes on during one of these audits? It’s not just a quick glance. It’s a meticulous, multi-stage process designed to leave no stone unturned.
Initial Scope Definition and Planning Setting the Audit Parameters
Before any technical work begins, the VPN provider and the auditing firm agree on the scope of the audit. This defines what exactly will be examined: is it just the no-logs policy, the entire server infrastructure, specific applications, or a combination? This stage also involves planning the timeline, resources, and access requirements for the auditors. It’s crucial for both parties to be clear on the objectives to ensure a comprehensive and effective audit.
Technical Assessments and Penetration Testing Deep Dive into Systems
This is where the heavy lifting happens. Auditors perform a variety of technical assessments:
- Vulnerability Scanning: Automated tools scan the VPN’s network and systems for known vulnerabilities.
- Penetration Testing: Ethical hackers attempt to exploit identified vulnerabilities, simulating real-world attacks to see if they can breach the system, access sensitive data, or disrupt services.
- Configuration Review: Auditors examine server configurations, firewall rules, and network settings to ensure they adhere to best security practices.
- Code Review: For applications, auditors may review the source code to identify potential flaws, backdoors, or insecure coding practices.
Policy and Process Review Examining Internal Operations
Beyond the technical aspects, auditors also scrutinize the VPN provider’s internal policies and processes. This includes:
- No-Logs Policy Verification: Reviewing internal documentation, interviewing staff, and examining data retention policies to confirm that no user-identifiable logs are being collected or stored.
- Data Handling Procedures: Assessing how user data (e.g., account information, payment details) is collected, stored, and protected.
- Incident Response Plans: Evaluating how the VPN provider handles security incidents and data breaches.
- Employee Access Controls: Checking who has access to what systems and data, and ensuring proper authentication and authorization mechanisms are in place.
Reporting and Remediation Documenting Findings and Fixing Issues
Once the assessments are complete, the auditing firm compiles a detailed report. This report typically includes:
- Executive Summary: A high-level overview of the findings.
- Detailed Findings: Specific vulnerabilities, misconfigurations, or policy discrepancies identified, along with their severity.
- Recommendations: Actionable advice on how to remediate the identified issues.
The VPN provider then works to address these recommendations. In many cases, a follow-up audit or re-test is conducted to confirm that the issues have been successfully resolved. The best VPNs will often publish a redacted version of these reports, demonstrating their commitment to transparency and allowing users to see the audit’s findings for themselves.
Benefits of Audited VPNs for Users Enhanced Security and Peace of Mind
So, why should you care if your VPN has been audited? The benefits are pretty significant, especially if you’re serious about your online privacy and security.
Increased Trust and Credibility Verifying Provider Claims
In an industry rife with marketing hype, independent audits cut through the noise. When a reputable third-party firm verifies a VPN’s no-logs policy or security infrastructure, it adds a layer of trust that self-assertions simply can’t provide. You’re not just taking their word for it; you have an expert’s confirmation. This is especially important for users in regions like the USA and Southeast Asia, where data privacy concerns are growing.
Reduced Risk of Data Leaks and Breaches Protecting Your Information
Audits are designed to identify vulnerabilities before they can be exploited. By undergoing regular security assessments, VPN providers can proactively fix weaknesses in their systems, reducing the risk of data leaks, IP leaks, or other security breaches. This means your personal information, browsing history, and online activities are better protected from snoopers, hackers, and even your own ISP.
Greater Transparency and Accountability Holding Providers Responsible
When a VPN provider commits to independent audits and publishes the results, they are demonstrating a strong commitment to transparency. This holds them accountable for their claims and encourages them to maintain high security standards. If issues are found, the public nature of the audit (even if redacted) pressures them to address these issues promptly. This level of accountability is vital for fostering a healthier and more trustworthy VPN ecosystem.
Informed Decision-Making Choosing the Right VPN for Your Needs
For you, the user, audited reports provide valuable information that helps you make an informed decision. You can compare VPNs not just on features and price, but also on their verified security and privacy posture. This allows you to choose a VPN that truly aligns with your security requirements, whether you’re a casual browser or someone who needs robust protection against surveillance.
Challenges and Limitations of VPN Audits What to Consider
While incredibly beneficial, it’s also important to understand that VPN audits aren’t a silver bullet. They come with their own set of challenges and limitations.
Cost and Frequency Audits Are Expensive and Not Always Regular
Independent audits are not cheap. Engaging a top-tier firm like PwC or Cure53 can cost tens of thousands, if not hundreds of thousands, of dollars. This high cost means that not all VPN providers can afford to conduct them, especially smaller ones. Furthermore, audits are typically snapshots in time. A VPN might be audited once a year, but vulnerabilities can emerge at any time. The infrequency of audits means there could be periods where the audited status doesn’t fully reflect the current security posture.
Scope Limitations Not Everything Is Always Audited
As mentioned earlier, the scope of an audit is defined beforehand. A VPN might boast about a 'no-logs audit,' but that doesn't necessarily mean their entire application suite or server infrastructure has been thoroughly vetted for security vulnerabilities. It's crucial to read the audit reports carefully to understand exactly what was covered and what wasn't. A limited scope means that while one aspect of the VPN might be verified, other critical components could remain unexamined.
Trust in the Auditor The Importance of Reputable Firms
The value of an audit heavily relies on the reputation and expertise of the auditing firm. If a VPN uses a lesser-known or unproven auditor, the credibility of the audit itself can be questioned. It’s important to look for audits conducted by well-respected cybersecurity firms or established accounting firms with a strong track record in security assessments. Without a trustworthy auditor, the audit report might not provide the assurance you’re looking for.
Human Element and Ongoing Security Beyond the Audit Report
Even the most thorough audit can’t account for every single variable. Human error, internal policy changes, or new zero-day vulnerabilities can emerge after an audit is completed. A VPN’s security is an ongoing process, not a one-time event. While audits provide a strong foundation, continuous internal monitoring, regular security updates, and a strong security culture within the VPN provider are equally important for maintaining long-term protection.
How to Interpret VPN Audit Reports What to Look For
So, you’ve found a VPN with an audit report. Great! But how do you actually read it and understand what it means for your security?
Check the Auditor’s Reputation Is the Firm Trustworthy
First things first: who conducted the audit? Look for names like PwC, Deloitte, Cure53, or Versprite. These firms have established reputations for independence and expertise. If the auditor is unknown or seems obscure, the credibility of the report might be questionable. A reputable auditor adds significant weight to the findings.
Understand the Scope What Was Actually Audited
Don’t just skim the headline. Dig into the report to see what exactly was audited. Was it just the no-logs policy? Or did it include the entire server infrastructure, specific applications, or a particular protocol? A comprehensive audit covering multiple aspects of the service provides more assurance than a narrow one. For example, an audit of a no-logs policy is great, but an audit that also includes penetration testing of the apps and servers is even better.
Look for Specific Findings and Recommendations What Issues Were Found
A perfect audit report with zero findings is rare and can sometimes even be a red flag (it might indicate a less thorough audit). What you want to see are specific findings, even minor ones, and clear recommendations for remediation. More importantly, look for evidence that the VPN provider has addressed these issues. The best providers will often include a section detailing how they’ve implemented the auditor’s recommendations, demonstrating their commitment to continuous improvement.
Review the Date of the Audit How Recent Is It
Security is an evolving landscape. An audit from five years ago, while better than nothing, isn’t as relevant as one conducted last year or even more recently. Look for the most recent audit reports to ensure that the VPN’s current systems and policies have been vetted. Regular, recurring audits are a strong indicator of a VPN provider’s ongoing commitment to security.
Public Availability Is the Report Accessible to Everyone
Transparency is key. The best VPNs will make their audit reports publicly available on their website, even if they are redacted to protect sensitive operational details. If a VPN claims to be audited but won’t share the report, that’s a red flag. Public availability allows you and other users to scrutinize the findings and hold the provider accountable.
The Future of VPN Audits Towards Greater Transparency and Accountability
The trend towards independent VPN audits is a positive one for the industry and for users. As digital privacy becomes an increasingly critical concern, the demand for verifiable security claims will only grow. We can expect to see more VPN providers embracing regular, comprehensive audits as a standard practice, rather than an exception.
This shift will likely lead to greater standardization in audit methodologies, making it easier for users to compare different VPN services based on objective security assessments. Furthermore, as technology evolves, audits will need to adapt to cover new protocols, features, and potential attack vectors. The ultimate goal is to create an environment where users can confidently choose a VPN, knowing that its claims have been rigorously tested and verified by independent experts, ensuring a safer and more private online experience for everyone.
:max_bytes(150000):strip_icc()/277019-baked-pork-chops-with-cream-of-mushroom-soup-DDMFS-beauty-4x3-BG-7505-5762b731cf30447d9cbbbbbf387beafa.jpg)